The year 2021 was challenging for the print sector. Lockdowns and restrictions caused a decrease in market demand for traditional print applications.
Additionally, wide format, light packaging, and label use expanded. Quickly switching their focus to other markets, businesses experienced rapid development.
The industry is showing clear signs of economic revival, which is good news. The year 2023 is predicted to be significantly better. Those who comply will benefit from new trends and play a more significant part in their customers’ success.
1. Digital Print Is Expanding Due To Shifting Supply Networks
A clear transition to eCommerce has occurred during the past 12 to 18 months. The expectation among consumers is now for record-breaking delivery timeframes.
Due to the increase in local manufacturing and the prolonged overseas shipping times, there is a greater demand for on-demand printing and label manufacturing. Customers are looking for environmentally friendly options.
With less trash and pollutants produced, digital printing is an excellent solution to this problem. Additionally, more environmentally friendly materials are used, resulting in lower client costs. What advantages does digital printing have for online shopping?
Compared to non-digital technologies, digital print gives significantly more versatility. This means that businesses can develop customized banners, signs, and more printing options using digital designs or innovative packaging with QR codes that can be scanned and shared.
Organizations will need to do this to fully capitalize on the advantages of drone-based delivery and real-time package tracking. Additionally, certain digital label presses are now able to create labels that are food-safe.
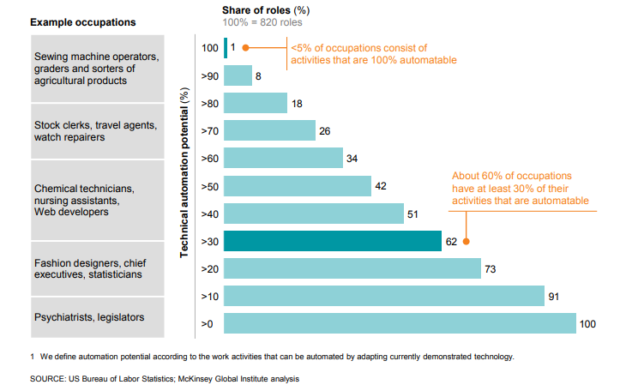
2. Automation Is Bringing Forth Efficiencies
Printers are already saving money and labor by automating print workflows and utilizing inline finishing equipment. Fewer people are needed to manage a job through to completion when operations are automated. As a result, printers can take on more work, provide clients with better results, and spend less money.
By automating their workflows, printers can manage orders round-the-clock and maximize the efficiency of their hardware. They can speed up printing and finishing, print on demand, enhance profitability, and provide new services to draw in new clients by streamlining prepress labor.
What does the future hold for automation? Automation will continue to spread in 2023 due to its advantages.
With the ability to offer more intricate services and outputs thanks to automated workflow adoption, printers may increase consumer demand without raising prices.
Margin expansion and the development of the company’s standing as a trustworthy, superior printer are benefits of doing this. Printing companies should focus on automating several critical processes, such as:
- web to print
- job submission / prepress
- color management
- variable data printing
- finishing
- device management
3. Design Solutions
A design staff is increasingly crucial for even the smallest printing businesses. Focusing on this business sector can help you stay competitive in the industry, whether you’re a single graphic designer or a large team. In addition, you may now generate income from logo and website design instead of relying simply on print revenue.
4. Digital Marketing
One of the most efficient marketing strategies accessible today is digital marketing. One looping piece of social media advertising can reach specific viewers for an unlimited period, making it the ideal example.
Social media advertising is just one aspect of digital marketing, though. It also provides extras like podcast production and website hosting. As a result, printing businesses that use these services can significantly increase their revenue in 2023.
5. Increase In Sustainable Printing
The rise in sustainable printing services is one trend that is likely to keep expanding over the coming few years. Eco-friendly technology is predicted to become increasingly commonplace in the sector by 2023.
These technologies, of course, offer a variety of other advantages in addition to being ecologically beneficial. They can boost your product’s quality while also offering a cost-effective option.
6. The Rise Of Digital Inkjet
This rise will be driven mainly by the printing industry, which has a higher demand for lightweight, manageable packaging that is also affordable.
To avoid sacrificing quality or speed, selecting an ink that can print on various substrates, including tissue or lightweight packaging, is crucial.
You only need a practical inkjet printer that can produce outstanding quality on various surfaces; you don’t want to spend money on pricey coatings or specialized digital stocks.
The sharp tool is LED UV inkjet technology. Due to the eCommerce industry’s continuous rapid growth, the need for various packaging choices will remain extremely strong through 2023 and beyond.

7. Direct Mail Marketing Campaigns
One of the most basic kinds of advertising is recognized to be direct mail marketing efforts. They are a reliable, efficient technique to bring in new clients while reasonably priced.
Direct mail marketing programs allow businesses to maintain brand awareness while influencing current or inactive clients.
8. Sustainability Will Have a Higher Priority
Many organizations now focus on minimizing their environmental impact; thus, manufacturers and channel partners must offer more environmentally friendly technological offerings.
Improved data analysis and reporting, circular goods and services, carbon data analysis, and process automation can contribute to sustainability. Switching clients from on-premise servers to cloud-based helps lower IT energy usage and associated carbon emissions.
Major Shifts in the Digital Printing Industry?
Growing technology has always provided more accessible, successful opportunities for companies to diversify their product lines.
Profit margins are predicted to rise considerably as digital technology becomes more efficient. Commercial printing companies are also trying to diversify to adjust how businesses manage their print marketing campaigns as they change.
As a result of the COVID-19 epidemic, which caused many print suppliers to experience commercial losses, they have begun to diversify their portfolio of goods and services rather than sticking to specific markets.
When you successfully meet your customers’ printing needs, they won’t need to look elsewhere for help with their print marketing initiatives.
Conclusion
Online digital printing’s convenience is a big draw for customers and businesses, and that trend is here to stay. The commercial printing sector has been completely transformed by the availability of internet uploads of photos and designs for picture albums, greeting cards, brochures, signage, and more.